DORA: Enhancing the financial sector’s digital operational resilience

WHY DID THE EU ADOPT DORA?
Cybersecurity and ICT Risks
Cybersecurity risks refer to the vulnerabilities and potential threats that can compromise the confidentiality, integrity, and availability of financial institutions’ digital assets, systems and data. If such risks materialise, they may compromise the security of the network and of information systems, of any technology dependent tool or process, of operations and processes, or of the provision of services by producing adverse effects in the digital or physical environment.
Disruptions to Critical services
Cyber-attacks could disrupt financial entities’ critical or important functions and materially impair their financial performance or the soundness or continuity of their services and activities. DORA requires financial institutions to develop strategies and capabilities to ensure uninterrupted service delivery, even in the face of severe operational disruptions. This includes comprehensive incident response plans and business continuity measures.
Ineffective cross-border cooperation to address cyber threats
Legislative disparities and uneven national regulatory or supervisory approaches with regard to ICT risk trigger obstacles to the functioning of the internal market in financial services, impeding the smooth exercise of the freedom of establishment and the provision of services for financial entities operating on a cross-border basis. Technology risks know no borders and the financial sector deploys its services on a wide cross-border basis within and outside the EU. Individual financial entities operating on a cross-border basis or holding several authorisations face operational challenges in addressing ICT risk and mitigating adverse impacts of ICT incidents on their own and in a coherent cost-effective way.

ICT Third-party risks
Financial institutions’ reliance on third-parties, such as cloud service providers or outsourcing partners, may give rise to ‘ICT third-party risk’. Such risks may arise for a financial institution in relation to its use of ICT services provided by ICT third-party service providers or by subcontractors of the latter, including through outsourcing arrangements.
Reporting and notification
Due to the ICT risk related provisions being only partially addressed at Union level, there are gaps or overlaps in important areas, such as ICT-related incident reporting and digital operational resilience testing, and inconsistencies as a result of emerging divergent national rules or cost-ineffective application of overlapping rules.
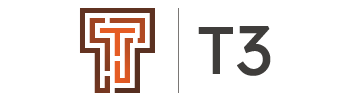
DORA: OVERVIEW
The Digital Operational Resilience Act (DORA), which came into force in January 2023, marks a significant regulatory milestone designed to bolster the operational resilience and IT security of the EU financial sector. As financial operations become increasingly reliant on digital technologies, the sector’s vulnerability to IT disruptions and cyber threats grows, making the enactment of DORA both timely and critical. By extending its reach to 20 different types of financial markets participants and ICT third-party service providers, like crediting rating services and data analytics providers, DORA establishes a single, binding and unified standard for managing digital risks and ensuring the stability of ICT systems used in finance. DORA’s provisions reflect a coordinated effort to safeguard the financial system’s integrity, ensuring that operational resilience is maintained in the face of potential digital disruptions that could have far-reaching consequences across borders and sectors.
AREAS OF COMPLEXITY
DORA involves several areas of complexity. Below are the most important ones:
Ongoing Cybersecurity Challenges
One of the key complexities in implementing DORA relates to addressing cybersecurity threats which are often dynamic and fast-moving. Financial institutions must constantly adapt to evolving cyber threats, stay vigilant against emerging risks, invest in cutting-edge security technologies, and establish robust incident response plans.
Broad Applicability
DORA applies to a wide range of financial entities, including banks, insurance companies, investment firms, and ICT third-party service providers. Such broad applicability ensures that the entire financial ecosystem, including its interconnected entities, adheres to consistent standards for operational resilience.
Operational Resilience
Operational resilience is a key focus of DORA, and achieving it involves extensive planning and testing. Financial institutions must develop comprehensive incident response plans and measures to ensure business continuity, to minimize downtime and to ensure the continuity of critical services in case of cyberattacks, natural disasters, or other unforeseen disruptions. Complexity mostly lies in coordinating and testing these measures to ensure they function as intended during high-stress scenarios.
Proportionate Implementation
Particularly for smaller financial institutions, determining what constitutes a proportionate response to DORA’s requirements, presents a significant challenge. Striking the right balance between implementing robust security measures and maintaining operational efficiency is crucial. Larger institutions may have more resources at their disposal, while smaller ones must ensure they meet regulatory requirements without overburdening their operations. Finding the right balance is no easy task and requires careful deliberation.
Senior Management Involvement
DORA imposes on institutions the obligation to identify and involve suitable Senior Management Function (SMF) holders in overseeing Model Risk Management (MRM) frameworks. Assigning responsibility for MRM and ensuring accountability at the highest levels of the organization is an intricate task. The complexity therefore lies in determining the most suitable SMF holders and ensuring their active participation in risk management.
Reporting and Audit Requirements
Meeting DORA’s stringent reporting and audit requirements demands meticulous record-keeping and efficient reporting mechanisms. Financial institutions must invest in robust data management systems and reporting tools to provide the necessary transparency and compliance documentation.
Resource Allocation
Efficiently allocating resources for cybersecurity enhancements, risk assessments, staff training, and technology upgrades while maintaining core operations is a demanding task. Financial institutions must carefully budget and prioritize their investments to ensure they meet regulatory requirements without compromising their overall financial stability. Striking the right balance between resource allocation and risk management is imperative, yet complex.
CONSEQUENCES FOR NON-COMPLIANCE
Failure to comply with DORA can lead to significant repercussions for financial institutions, including stringent regulatory sanctions. According to Article 50 of DORA, the competent authorities of EU Member States must have at the very least the powers to issue cease and desist orders, impose pecuniary penalties, issue public notices and statements. Sanctions against natural persons, like members of a financial institution’s management body, are also foreseen. Member States may choose to opt for criminal law enforcement.
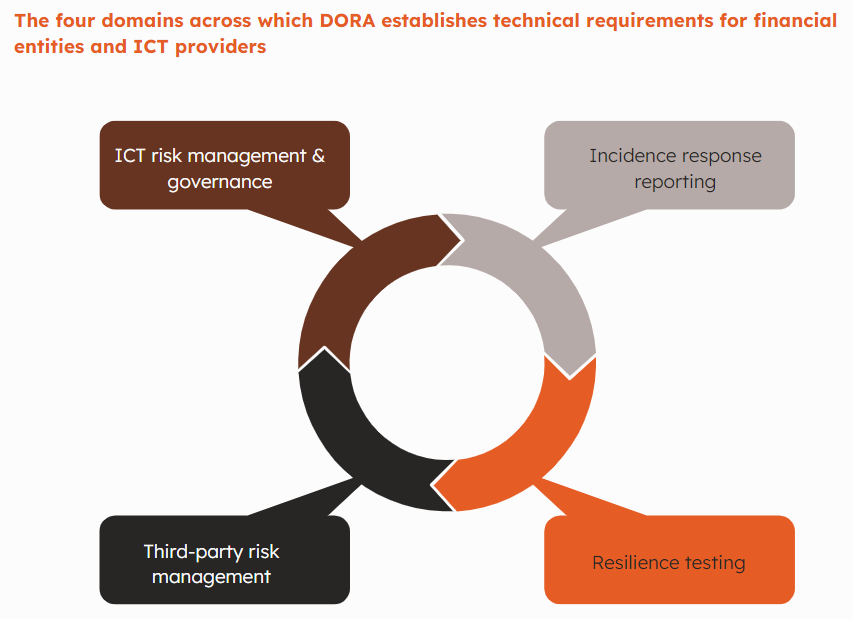
IMPORTANT DEADLINES
DORA came into force on 16 January 2023, with application starting from 17 January 2025. The two-year window is crucial for financial institutions to align with DORA’s requirements, develop compliance frameworks, and enhance operational resilience.
Besides the main Act, the three ESAs’ (EBA, ESMA, EIOPA) are mandated with drafting regulatory technical (RTSs) and implementing technical standards (ITSs). These are expected to be finalized in the course of 2024.
SERVICES
“This publication has been prepared for general guidance on matters of interest only, and does not constitute professional advice. You should not act upon the information contained in this publication without obtaining specific professional advice. No representation or warranty (express or implied) is given as to the accuracy or completeness of the information contained in this publication, and, to the extent permitted by law, T3 Consultants Ltd, its members, employees and agents do not accept or assume any liability, responsibility or duty of care for any consequences of you or anyone else acting, or refraining to act, in reliance on the information contained in this publication or for any decision based on it.